This type of authentication has been around since about 2017 timeframe with OAuth v1 and now has updated with OAuth2. I worked with doing some OAuth calls when I was in EXO CSS at Microsoft. I wanted to pass this Exchange Team Blog article along since it has come out with updates recently.
Since we announced in 2019 that we would be retiring Basic Authentication for legacy protocols we have been encouraging our customers to switch to Modern Authentication. Modern Authentication, based on OAuth2, has a lot of advantages and benefits as we have covered before, and we’ve yet to meet a customer who doesn’t think it is a good thing. But the ‘getting there’ part might be the hard part, and that’s what this blog post is about.
This post is specifically about enabling Modern Authentication for Outlook for Windows. This is the client most widely used by many of our customers, and the client that huge numbers of people spend their day in. Any change that might impact those users is never to be taken lightly.
As Admin, you know you need to get those users switched from Basic to Modern Auth, and you know all it takes is one PowerShell command. You took a look at our docs, found the article called Enable or disable Modern Authentication for Outlook in Exchange Online | Microsoft Docs and saw that all you need to do is read the article (which it says will take just 2 minutes) and then run:
Set-OrganizationConfig -OAuth2ClientProfileEnabled $true
That sounds easy enough. So why didn’t you do it already?
Is it because it all sounds too easy? Or because there is a fear of the unknown? Or spiders? (We’re all scared of spiders, it’s ok.)
We asked some experts at Microsoft who have been through this with some of our biggest customers for their advice. And here it comes!
Expert advice and things to know
“Once Exchange Online Modern Authentication is enabled for Outlook for Windows, wait a few minutes.”
That was the first response we got. It was certainly encouraging, but wasn’t exactly a lot of information we realized, so we dug in some more, and here’s what we found.
One thing you need to remember that enabling Modern Authentication for Exchange Online using the Set-OrganizationConfig parameter only impacts Outlook for Windows. Outlook on the Web, Exchange ActiveSync, Outlook Mobile or for Mac etc., will continue to authenticate as they do today and will not be impacted by this change.
- Outlook 2010 or older clients that can’t support Modern Authentication will continue to use basic authentication (you enable Outlook to use modern, this does not disable basic auth)
- Outlook 2013 will need a registry key change to use Modern Auth.
- Outlook 2016 or newer has the registry key already set, but it could be disabled, so if those versions are still using Basic after the change, check that out.
- The Office cloud policy service lets you enforce policy settings for Microsoft 365 Apps for enterprise (previously named Office 365 ProPlus) on a user’s device, even if the device isn’t domain joined or otherwise managed. You can potentially use this to control registry keys for non-domain joined machines.
- To check which Outlook for Windows supports Modern Authentication see How Modern Authentication works for Office 2013 and Office 2016 client apps – Microsoft 365 Enterpri…
- If you have multiple mailboxes in one Outlook profile, and one is an on-premises mailbox and is still using RPC, and the other is in Exchange Online, you might see an issue. Explained here: Outlook prompts for password when Modern Authentication is enabled – Outlook | Microsoft Docs
Once Modern Authentication is turned on in Exchange Online, a Modern Authentication supported version of Outlook for Windows will start using Modern Authentication after a restart of Outlook. Users will get a browser-based pop up asking for UPN and Password or if SSO is setup and they are already logged in to some other services, it should be seamless.
If the login domain is setup as Federated, the user will be redirected to login to the identity provider (ADFS, Ping, Okta, etc.) that was set up. If the domain is managed by Azure or set up for Pass Through Authentication, the user won’t be redirected but will authenticate with Azure directly or with Azure on behalf of your Active Directory Domain Service respectively.
Take a look at your Multi-Factor Authentication (MFA)/Conditional Access (CA) settings. If MFA has been enabled for the user and/or Conditional Access requiring MFA has been setup for the user account for Exchange Online (or other workloads that have a dependency on Exchange Online), then the user/computer will be evaluated against the Conditional Access Policy.
- Here is an example of a CA policy with Condition of Client App “Mobile apps and desktop clients”. This will impact Outlook for Windows with Modern Authentication whereas “Other Clients” would impact Outlook for Windows using Basic Authentication, for example.
Next is Access Control Grant in CA requiring MFA. If Outlook for Windows was using Basic Authentication, this would not apply since MFA depends on Modern Authentication. But once you enable Modern Authentication, users in the scope of this CA policy would be required to use MFA to access Exchange Online.

The Modern Authentication setting for Exchange Online is tenant-wide. It’s not possible to enable it per-user, group or any such structure. For this reason, we recommend turning this on during a maintenance period, testing, and if necessary, rolling back by changing the setting back to False. A restart of Outlook is required to switch from Basic to Modern Auth and vice versa if roll back is required.
It may take 30 minutes or longer for the change to be replicated to all servers in Exchange Online so don’t panic if your clients don’t immediately switch, it’s a very big infrastructure.
Be aware of other apps that authenticate with Exchange Online using Modern Authentication like Skype for Business. Our recommendation is to enable Modern Authentication for both Exchange and Skype for Business.
Here is something rare, but we have seen it… After you enable Modern Authentication in an Office 365 tenant, Outlook for Windows cannot connect to a mailbox if the user’s primary Windows account is a Microsoft 365 account that does not match the account they use to log in to the mailbox. The mailbox shows “Disconnected” in the status bar.
This is due to a known issue in Office which creates a miscommunication between Office and Windows that causes Windows to provide the default credential instead of the appropriate account credential that is required to access the mailbox.
This issue most commonly occurs if more than one mailbox is added to the Outlook profile, and at least one of these mailboxes uses a login account that is not the same as the user’s Windows login.
The most effective solution to this issue is to re-create your Outlook profile. The fix was shipped in the following builds:
- For Monthly Channel Office 365 subscribers, the fix to prevent this issue from occurring is available in builds 16.0.11901.20216 and later.
- For Semi-Annual Customers, the fix is included in builds 16.0.11328.20392 (Version 1907) and later.
You can find more info on this issue here and here.
That’s a list of issues we got from the experts. Many customers have made the switch with little or no impact.
How do you know Outlook for Windows is now using Modern Auth?
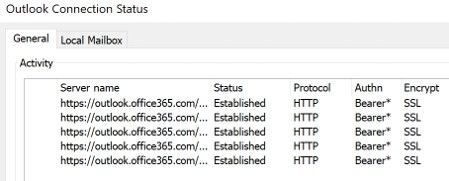
When using Basic Auth, the Outlook Connection Status “Authn” column shows “Clear*”

Once you switch to Modern Auth, the Connection Status in Outlook showing Modern Authentication “Authn” column shows “Bearer*”
And that’s it!
The biggest thing to check prior to making the change are your CA/MFA settings, just to make sure nothing will stop access from happening and making sure your users know there will be a change that might require them to re-authenticate.
Now you know what to expect, there is no need to be afraid of enabling Modern Auth. (Spiders, on the other hand… are still terrifying, but that’s not something we can do much about.)
REFERENCES:
Enabling Modern Auth for Outlook – How Hard Can It Be? – Microsoft Tech Community
Enable or disable modern authentication for Outlook in Exchange Online | Microsoft Docs

One thought on “Enabling Modern Authentication for Outlook – How Hard Can It Be?”
Comments are closed.